What is Plookup?
Plookup was described by the original authors in [GW20] as a protocol for checking whether values of a committed polynomial, over a multiplicative subgroup of a finite field , are contained in a vector that represents values of a table . More precisely, Plookup is used to check if certain evaluations of some committed polynomial are part of some row of a lookup table . One particular use case of this primitive is: checking whether all evaluations of a polynomial , restricted to values of a multiplicative subgroup , fall in a given range . i.e., proving that, for every , we have . Plookup’s strategy for soundness depends on a few basic mathematical concepts described below.Notations and preliminaries
Sets and multisets
Recall that a set is a collection of distinct objects, called elements, where repetitions and order of elements are disregarded. That is, the set is the same set as . Yet, as multisets, is not the same as It is because multisets take into consideration all instances of an element. Given a multiset , we define multiplicity to be the number of all instances of an element. So, in the multiset ; the element has multiplicity 1, while is of multiplicity 2 , and lastly, has multiplicity 3. A set can therefore be described as a collection of distinct objects where multiplicity and ordering of objects have no significance. Multisets are similar to sets in that they also do not respect the ordering of elements. That is, and represent the same multiset, because they both contain the same elements, each with the same multiplicity. Given multisets and , can be sorted by as follows, . That is, ” sorted by ” means the elements of are ordered according to the order they appear in , without losing their multiplicity.Sorted multisets and set differences
Unless otherwise stated, all sorted multisets are henceforth sorted by , where is the set of natural numbers . For any given sorted multiset , define the set of differences of as the set of non-zero differences . That is, zero-differences, , are discarded. Take as examples the following sorted multisets: , and . These three multisets have the same set of differences, which is . Although has the same set of differences as and , note that the differences appear in a different order; 4 appeared first then 2.Testing for containment
Let and be ordered multisets, and none of the elements of are repeated. It can be observed that:- If and , then and have the same set of differences and the differences appear in the same order.
- If and have the same set of differences except for the differences’ order of appearance, then .
- If and have the same set of differences and the differences appear in the same order, then .
- The equality of the sets of differences, and
- The order in which the differences () appear in both multisets are the same.
Testing for repeated elements
Consider again the ordered multisets: and . If has some repeated elements, for some , then these can be tested by comparing randomized sets of differences. A randomized set of differences related to is created by selecting a random field element and defined as the set . So, instead of a pair of repeated elements yielding a difference of zero because , they yield in the setting of randomized set of differences. This property of repeated elements yielding a multiple of , characterizes repeated elements in ordered multisets. Consequently, when computing randomized set of differences, repeated elements can be identified by these multiples of . A test can therefore be coined using a grand product argument akin to the one used in PLONK’s permutation argument [GWC19].Vectors
The above concepts defined for multisets apply similarly to vectors, and the Plookup protocol also extends readily to vectors. A vector is a collection of ordered field elements, for some finite field , and it is denoted by . A vector is contained in a vector , denoted by , if each for . The vector of differences of a given vector is defined as the vector , which has one less component (or element) compared to . That is, because . Given a random scalar in a field and a vector , a randomized vector of differences of is defined as . The concatenation of vectors and is the vector , and it has components.Plookup protocol
The context of Plookup is within a polynomial commitment scheme, where a party ,called the prover, seeks to convince the second party , called the verifier, that it knows a certain polynomial. The protocol, as described in the Plookup paper, mentions a third party called the Ideal party, denoted by , which is also called the trusted party. It is this trusted party who is responsible for generating all the proof-verification system parameters. Among these parameters are the so-called preprocessed polynomials. In the case of a non-interactive proof-verification system, the trusted party is equipped so as to act as an intermediary between the prover and the verifier.- The protocol starts with the generation of preprocessed polynomials and describing them as a Lookup Table.
- Prover submits messages in the form of polynomials expressed either as multisets or vectors.
- The verifier also sends randomly selected field elements , called challenges.
- The prover then evaluates a special polynomial on the ‘s and sends them to .
- The verifier subsequently requests to check if certain polynomial identities hold true.
- The verifier accepts the prover’s submissions as true if all identities hold true, otherwise it rejects.
Plookup optimization strategies
- Using randomized sets of differences.
- Soundness is backed by the Schwarz-Zippel lemma.
- Deploying the grand product argument which describes the polynomials and appearing in the polynomial identities.
- Concatenation of witness vectors with the LUT vectors.
Plookup in PIL
The test for whether the polynomial identities hold true, is based on the following lemma (viz. Claim 3.1 as stated and proved in pages 4 and 5 of the Plookup paper). The polynomial identities hold true if, and only if, and , which is the concatenation of and , is sorted by . A Plookup applies to Polynomial Commitment Scheme settings, where the polynomials are expressed as vectors; , and . It is therefore a test of inclusion, denoted by . In the zkEVM setting, Plookup typically appears in PIL code as: where "" is a PIL keyword for set inclusion, .Application of Plookup in PIL
In the generic state machine, recall polynomials that define instructions; , , , , , , , , and . The polynomials; , , and ; are only used during execution, and therefore do not form part of the instructions. When verifying correct execution, there is a need to check if the combination of committed polynomials, is one of the valid combinations of the ROM instructions, PIL uses Plookup to carry out this check. This appears at the last three lines of the PIL code for the generic state machine, shown in the figure below. Recall that the ROM’s polynomial counterpart to the is the .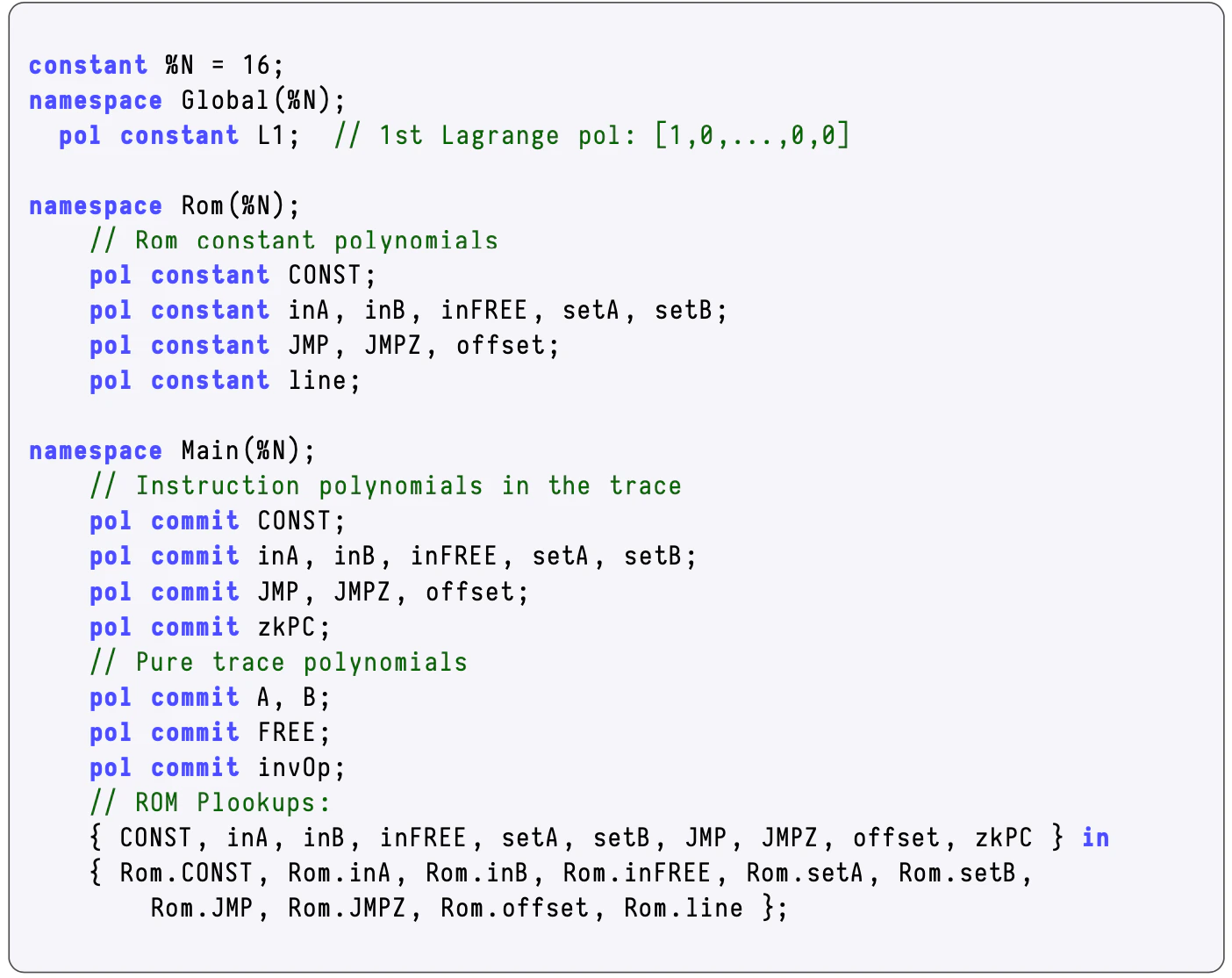
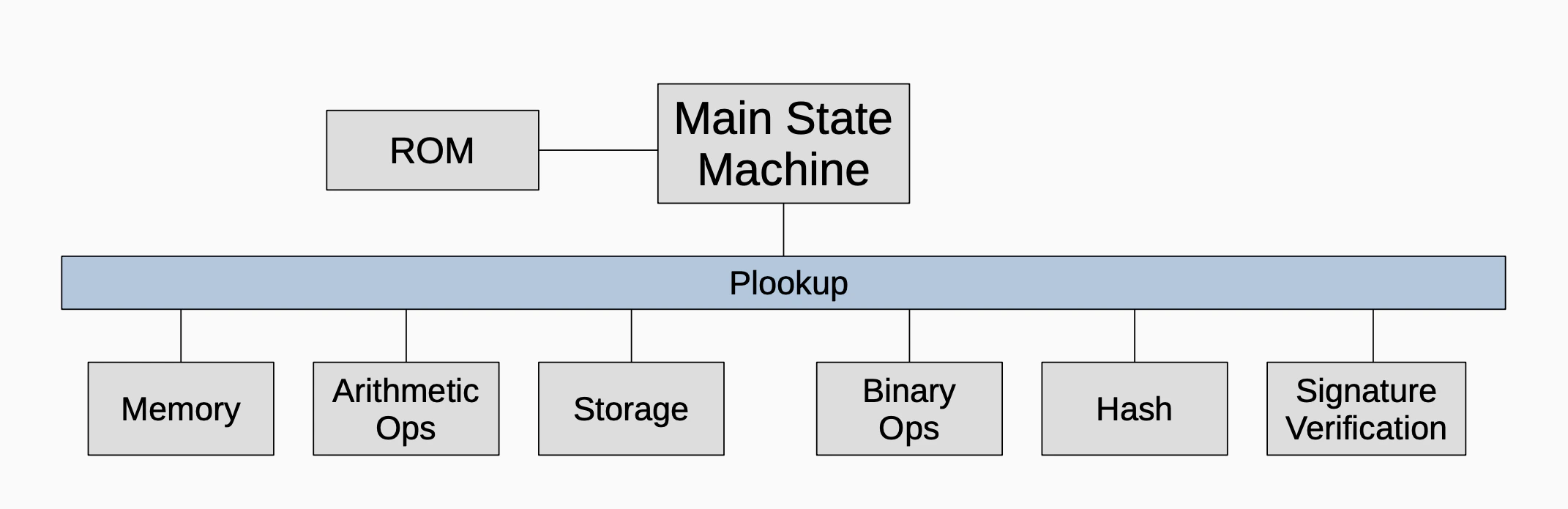
Role in zkEVM
Plookup instructions appear in the PIL codes of state machines in the zkEVM. Plookup is used by some state machines to ensure that certain output values are included in a given lookup table. Plookup is useful when set inclusion must be verified. The diagram below depicts the extensive role that Plookup plays in the zkProver’s secondary state machines.