Building the zkEVM STARK
The first step in building the zkEVM STARK is to build the ROM of the zkEVM state machine, where this ROM is nothing but a program containing instructions for the executor to generate a specified execution trace of the zkEVM. And it is written in JSON as rom.json. The PIL code, zkevm.pil, is built for validating the execution trace. The executor uses both the rom.json and zkevm.pil to generate all the constant polynomials for the execution trace of the zkEVM, rom.const. Observe that, as previously mentioned, committed polynomials are not needed in the setup phase, so at this stage there is no need to run the executor of the zkEVM in order to generate them. See the below schematic diagram of the process used when building a zkEVM STARK.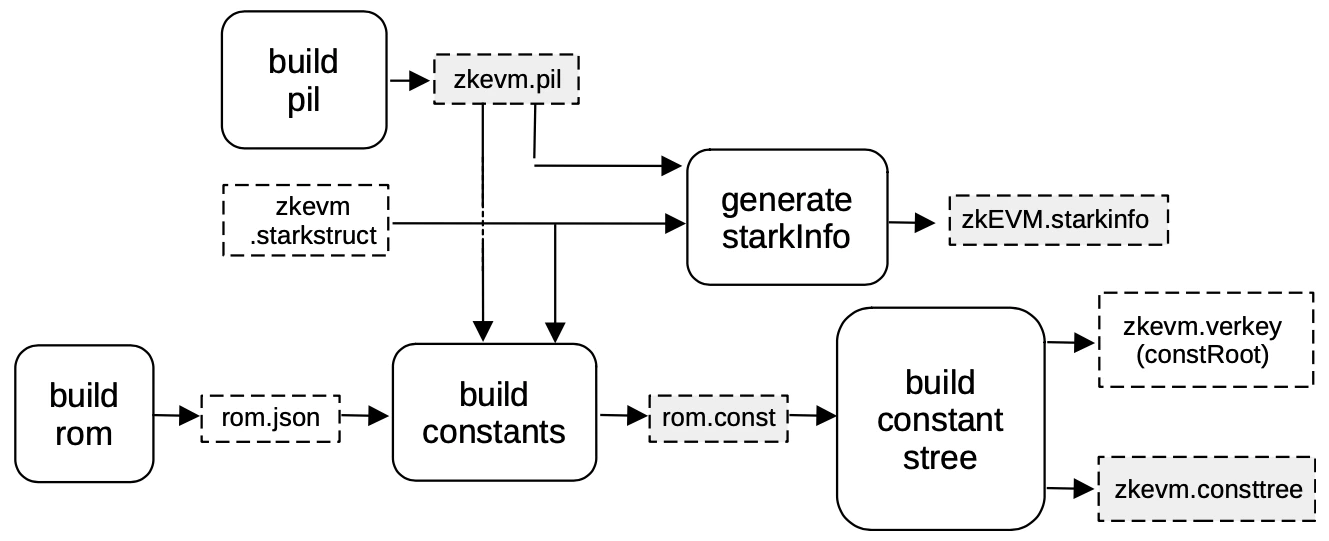
Setup S2C for zkEVM STARK
The next step in the setup phase is to generate the circuit that verifies the zkEVM STARK (see the below Figure).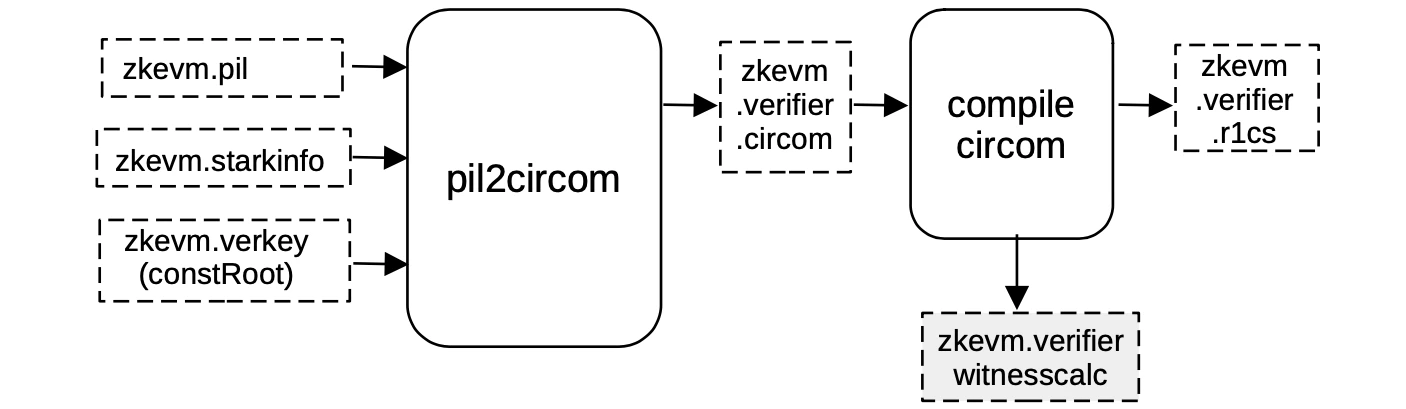
- polynomial names,
- the zkevm.starkinfo file which specifies the blowup factor,
- the number of queries,
- the steps of the FRI-verification procedure,
- the constRoot in the zkevm.verkey file,
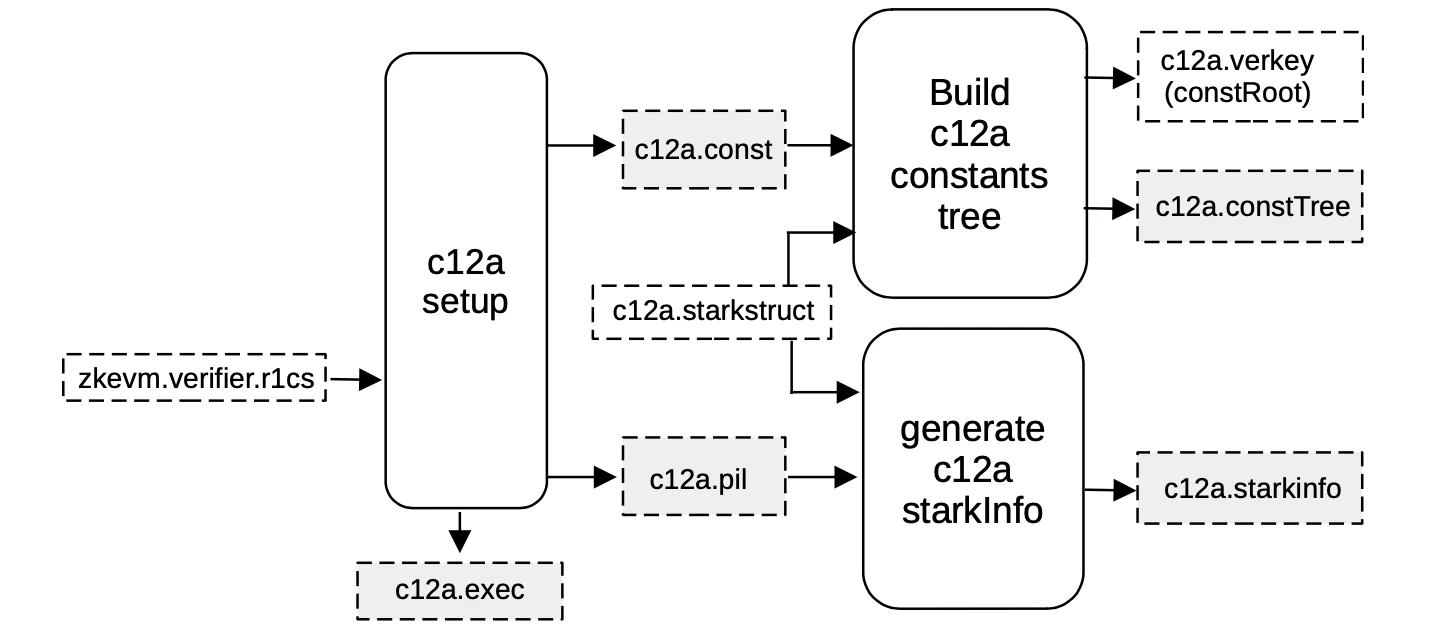
Setup c12a
The zkEVM STARK is verified by a circuit called zkevm.verifier. This is the c12a circuit previously seen in the compression stage, at the beginning of the Proving Architecture. It is so called because the PIL code that verifies the c12a circuit, is a PlonKish circuit with custom gates and polynomials, aiming at compression.